Security By Design- Part 11
Contributors

The U.S. Cybersecurity and Infrastructure Security Agency defines “Secure by Design” to mean that technology products are built in a way that reasonably protects against malicious cyber actors successfully gaining access to devices, data, and connected infrastructure.
This is a very concise statement, with a focus on the design of technology-based systems. In the real and practical world we live in, focusing only on the security design aspects of complex digital systems or the components that complex digital systems are made of will ensure that your digital business world will be insecure.
Security focusing only on Design aspects of Complex Systems will ensure Cyber Insecurity
My personal views about Security by Design are well known by those who have worked with me or have been my clients throughout my career. Our digital systems do not stand alone as technology systems only. As soon as we deploy technology, the technology enters the realm of becoming a system, interconnecting, and interacting with other systems with which our business operates. These business systems are comprised of benevolent technology, people, and processes interconnecting our business with our customers and suppliers, as well as the shared open systems we use, such as the World Wide Web and the Internet. Unfortunately, bad actors also use the open and shared internet and World Wide Web systems with the sole purpose to compromise our business operations. So, … focusing only on the secure design of technology products is not enough to secure our Businesses by Design.
Focusing only on the secure design of technology products is not enough to secure our Businesses by Design
Securing our Business by Design requires hyper-attentiveness to the security of the complex digital systems environment of Technology, Data, Processes, and People.
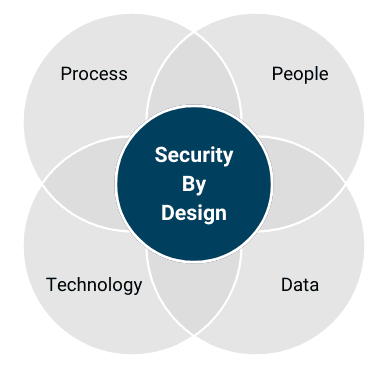
By the very nature of how complex digital systems work, Security by Design requires that all aspects of security design and operations work in concert continually. Any gaps, mistakes, or lack of attentiveness by those who use, support, or operate our systems, including those responsible for oversight and assurance, will guarantee a cybersecurity compromise.
Security by Design
- Technology / Data
- Technology / Process
- Technology / People
- People / Process
- People / Data
- Data / Process
The February 2024 “cyberattack” triggered a shutdown of Change Health Care’s electronic medical claims processing systems, leaving doctors and other providers of medical care (pharmacies, rehabilitation facilities, etc.) without the ability to obtain insurance approval for patient services, and thus not receive payment for medical services, was a failure of the People / Process / Technology aspects of Security by Design. It has been reported that an absence of multi-factor authentication reportedly left a remote access application exposed. The actual bad actor access has been confirmed to have occurred using compromised user credentials via the remote access application. But I ask, is this the true or root failure in this incident?
Is the lack of two-factor authentication the root cause of the Change in Health Care Cyber Attack?
From my perspective, the root cause of this cybersecurity failure is found in the Process / People domain of Security by Design. This is a classic failure of people not utilizing audit/controls processes and/or using the appropriate process but not paying attention to the audit/controls information the process identified. Indeed, Change Health Care is a relatively recent acquisition of OPTUM, which is a subsidiary of United Health Care. Prior audits have reportedly highlighted the lack of two-factor authentication at Change Health Care, but this information, it seems, was not acted upon. This was highlighted by Andrew Witty, CEO of United Health Group, who testified at a U.S. Senate Finance Committee hearing examining cyber-attacks on health care and the Change Healthcare attack on May 01, 2024. The cyber-attack has become the costliest in U.S. history. Healthcare Financial Management Association, the auditor for financial analysis of the losses, so far is reporting an expected $6.87 billion in total losses from this breach (including equity loss, legal fees, regulatory fines, class action claims, PR expenses, notification costs, and other expenses). $6.87 Billion in Losses + nearly 1/3 of all Americans impacted!
Joseph F. Norton is a Risk, Security, and Crisis Management professional.
He is a founding member and Qualified Technology Executive of the Digital Directors Network, Chair of the Advisory Board with Next Era Transformation Group, and Chief Security Officer with APF Technologies.
He has served as Chief Security Officer, SVP at Atos, Chief Technology Officer and Head of Operations, SVP at Philips, Chief Technology Officer, SVP at Novartis, Executive-in-Residence with McKinsey & Company, and Chief Technology Officer at McDonald’s. He has also held professional roles during his career with JPMorgan Bank, Oracle, Sybase and Grumman Aerospace Corporation, and the United States Navy.
Other Popular Articles
In the digital age, businesses must adopt an ad
GRC is the capability, or integrated collection